GDPR compliance requires organizations to protect personal data through transparency, strong security controls, informed consent, and respect for user rights such as access and erasure. It is both a regulatory framework and a cybersecurity standard that defines how personal data should be collected, processed, stored, and protected.
In cybersecurity terms, GDPR pushes organizations to move from reactive data protection to a proactive, risk-based security model where privacy is built into every layer of the system.
Key GDPR Compliance Requirements
1. Lawful, Fair, and Transparent Processing
Every organization must have a valid legal basis for processing personal data. This could include consent, contractual necessity, legal obligations, or legitimate interest.
From a cybersecurity perspective, transparency also means:
- Clearly documenting data flows
- Maintaining audit trails of data processing activities
- Ensuring users understand how their data moves across systems
Organizations must ensure that individuals are not misled and that data usage is clearly communicated through privacy notices.
2. Consent Management and User Control
Consent is a central pillar of GDPR compliance. It must be:
- Freely given (no pressure or forced agreement)
- Specific (linked to a clear purpose)
- Informed (users understand what they are agreeing to)
- Unambiguous (clear affirmative action required)
From a security standpoint, consent management systems must:
- Log consent history securely
- Allow real-time updates or withdrawals
- Ensure backend systems immediately reflect consent changes
This ensures data processing is always aligned with user permission.
3. Core Data Protection Principles
GDPR enforces foundational principles that directly shape cybersecurity practices:
Data Minimization
Only collect data that is strictly required for the intended purpose. Excess data increases breach risk.
Purpose Limitation
Data must not be reused for unrelated activities without additional consent or legal basis.
Accuracy
Organizations must maintain correct and updated data to avoid operational and legal risks.
Storage Limitation
Personal data should not be retained indefinitely. Secure deletion or anonymization must be enforced when data is no longer required.
Integrity and Confidentiality
This is the cybersecurity core of GDPR and includes:
- Encryption at rest and in transit
- Secure authentication mechanisms
- Access control policies
- Protection against unauthorized access or data loss
4. Data Subject Rights
GDPR gives individuals strong control over their personal data. Organizations must build systems that support these rights efficiently:
- Right to Access: Users can request copies of their data
- Right to Rectification: Incorrect data must be corrected
- Right to Erasure: Data can be deleted upon request (“right to be forgotten”)
- Right to Restrict Processing: Limits how data is used
- Right to Data Portability: Data must be transferable in a structured format
From a cybersecurity angle, systems must be designed to retrieve, modify, or delete data securely without exposing it to unauthorized parties during the process.
5. Data Protection Officer (DPO)
Organizations involved in large-scale monitoring or processing of sensitive data must appoint a Data Protection Officer.
The DPO role includes:
- Monitoring GDPR compliance
- Advising on data protection impact assessments
- Acting as a point of contact for regulators
- Ensuring internal cybersecurity policies align with GDPR
This role acts as a bridge between legal compliance and technical security teams.
6. Breach Notification and Incident Response
One of the most critical cybersecurity requirements under GDPR is breach management.
Organizations must:
- Detect and contain breaches quickly
- Assess risk impact on personal data
- Notify supervisory authorities within 72 hours of awareness
- Inform affected individuals if there is high risk
A strong incident response framework typically includes:
- Continuous monitoring systems
- Security Information and Event Management (SIEM) tools
- Defined escalation procedures
- Post-incident forensic analysis
7. Privacy by Design and Default
GDPR requires privacy to be embedded into systems from the beginning, not added later.
This means:
- Security controls integrated during system development
- Default settings that protect user privacy
- Minimal data exposure by design
- Regular security testing during development lifecycle
In cybersecurity, this aligns with Secure SDLC practices and DevSecOps approaches.
8. International Data Transfers
When personal data is transferred outside the EU/EEA, it must be protected with adequate safeguards.
These include:
- Standard Contractual Clauses (SCCs)
- Adequacy decisions by the EU Commission
- Strong encryption and access controls during transfer
This ensures that data remains protected even across jurisdictions with different privacy laws.
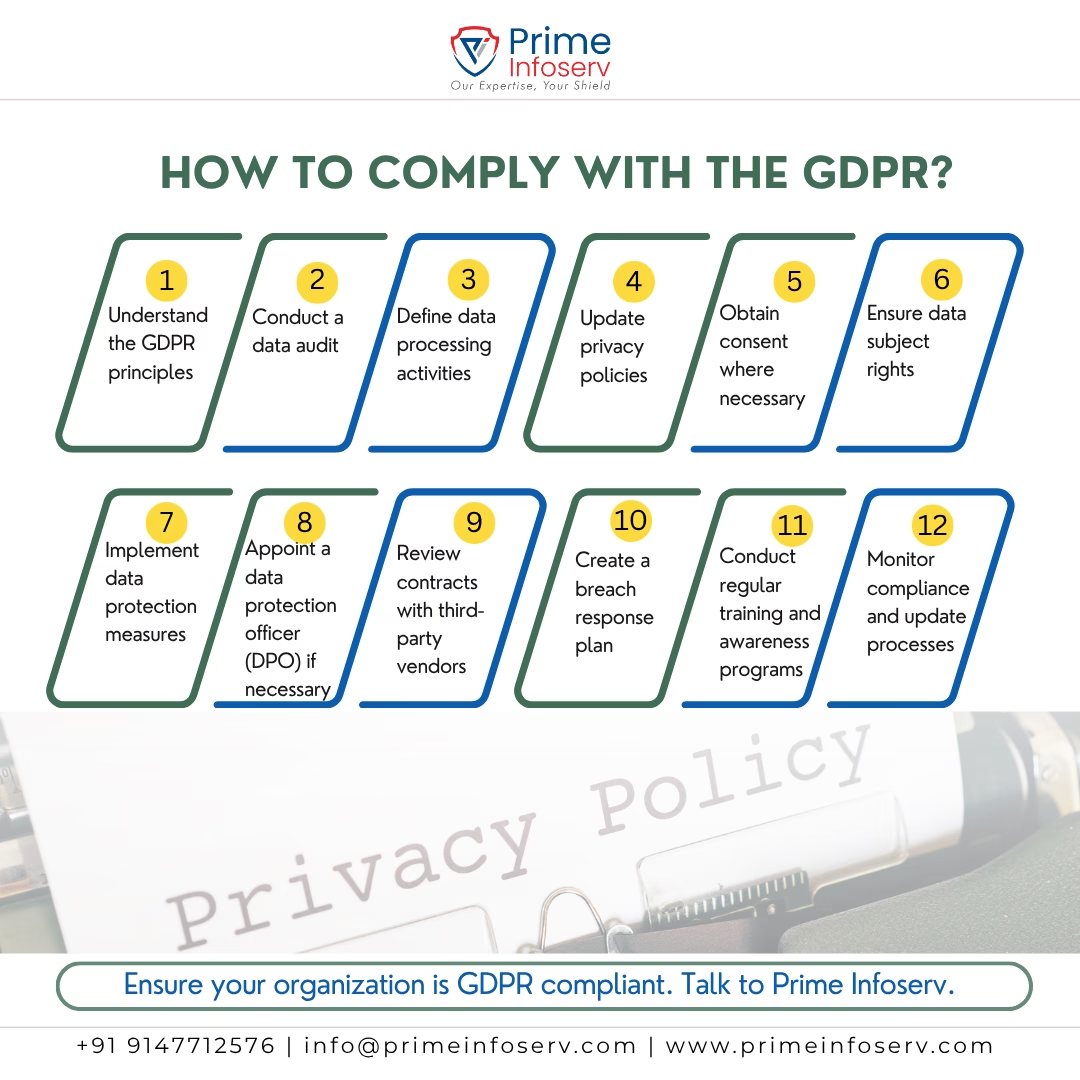
Steps for GDPR Compliance Implementation
1. Conduct a Data Inventory Audit
Organizations must first understand:
- What personal data is collected
- Where it is stored
- Who has access to it
- How long it is retained
This forms the foundation of all compliance efforts.
2. Update Privacy Policies
Privacy policies should clearly explain:
- Data collection practices
- Purpose of processing
- User rights
- Contact points for data concerns
Clear communication builds trust and ensures transparency.
3. Strengthen Security Measures
Cybersecurity controls should include:
- Encryption of sensitive data
- Pseudonymization techniques
- Multi-factor authentication
- Regular vulnerability assessments
- Secure backup and recovery systems
4. Vendor and Third-Party Compliance
Third-party risk is a major GDPR concern. Organizations must ensure:
- Formal Data Processing Agreements (DPA)
- Security assessments of vendors
- Continuous monitoring of third-party access
5. Employee Awareness and Training
Human error remains one of the biggest risks in data breaches. Regular training should cover:
- Data handling procedures
- Phishing awareness
- Secure access practices
- Incident reporting mechanisms
Conclusion
GDPR compliance is not just about meeting regulatory requirements—it is about building a secure, transparent, and accountable data protection ecosystem. When aligned with cybersecurity practices, it helps organizations reduce breach risks, improve governance, and strengthen user trust.
A mature GDPR implementation transforms security from a reactive function into a proactive, structured, and resilient framework.
If you want to understand how strong your current data protection and cybersecurity posture is, a GDPR Readiness Assessment by Prime Infoserv can help you:
- Identify compliance gaps
- Evaluate cybersecurity weaknesses
- Improve data governance practices
- Build a clear roadmap toward full GDPR alignment
Take the next step toward stronger compliance and cybersecurity resilience with a GDPR Readiness Assessment. Call +91 9147712576 or Mail: info@primeinfoserv.com





