A whaling attack is a highly targeted form of whaling phishing and closely linked to business email compromise (BEC). In this attack, cybercriminals impersonate senior executives—such as CEOs or CFOs—to manipulate employees or leadership into transferring funds, sharing sensitive data, or granting system access.
These attacks rely heavily on social engineering, authority, and urgency—making them far more dangerous than generic phishing attempts.
Whaling Attack vs Phishing vs Spear Phishing
- Phishing: Mass, generic emails sent to large groups
- Spear Phishing: Targeted messages using personal or company-specific data
- Whaling Attack: A highly focused version of spear phishing aimed at top executives, often within BEC attack scenarios
Business Risks of Whaling Attacks
- Financial Loss: Unauthorized transfers and fraudulent payments
- Data Breach: Exposure of employee, financial, or customer data
- Reputation Damage: Loss of trust, compliance issues, and legal consequences
Real-Life Examples of Whaling Attacks
1.Ubiquiti Networks (2015) – $47 Million Loss
Ubiquiti Networks fell victim to a sophisticated executive impersonation scam. Attackers sent emails to the finance department pretending to be senior executives and external partners.
- The emails referenced real business processes and vendors
- Employees were instructed to process urgent wire transfers
- The request seemed legitimate because it matched ongoing transactions
By the time the fraud was discovered, the company had already transferred $47 million to attacker-controlled accounts. This case is a classic example of how BEC attacks exploit trust and routine workflows.
2.FACC, Crelan Bank & Leoni AG (2016) – Multi-Million Dollar Impact
Several major organizations reported similar incidents:
- FACC (Austria): Lost ~$54 million due to fake executive instructions
- Crelan Bank (Belgium): Lost ~$76 million in a CEO fraud scheme
- Leoni AG (Germany): Lost ~$40 million through fraudulent payment requests
In each case:
- Attackers studied internal communication patterns
- Emails appeared to come directly from top executives
- Employees followed instructions without secondary verification
The aftermath included financial losses, leadership changes, and reputational damage.
3.Snapchat (2016) – Payroll Data Breach
In this incident, a payroll employee received an email that appeared to come from the CEO requesting sensitive employee payroll information.
- The tone was urgent and authoritative
- No technical malware was required—just pure social engineering
- The employee complied, believing it was a legitimate executive request
As a result:
- Confidential payroll data was exposed
- The case was reported to authorities
- Affected employees were offered identity theft protection services
4.Seagate (2016) – Tax Data Exposure
A similar tactic was used against Seagate, where attackers targeted a senior executive:
- The attacker requested W-2 tax forms of employees
- The request appeared legitimate and aligned with internal processes
- The executive unknowingly shared sensitive tax data
Impact:
- Employees became vulnerable to tax fraud and identity theft
- The incident had to be reported to regulatory authorities
5.Mattel (2019) – $3 Million Fraud Attempt
Mattel faced a direct CEO impersonation attempt targeting its finance team:
- An email appeared to come from the CEO requesting a high-value fund transfer
- The request created urgency and bypassed normal procedures
- A senior finance executive approved the transaction
The company managed to recover a portion, but still suffered millions in losses, highlighting how even large enterprises can be deceived.
6.Fake Legal Subpoena Attack – Malware Delivery
In a more advanced and creative case:
- Executives received emails claiming to be from a legal authority (court subpoena)
- The message included accurate personal and professional details
- A link was provided to “view the subpoena”
However:
- The link installed malware on the system
- Attackers gained deeper access to corporate networks
This shows how attackers combine psychological pressure + technical compromise.
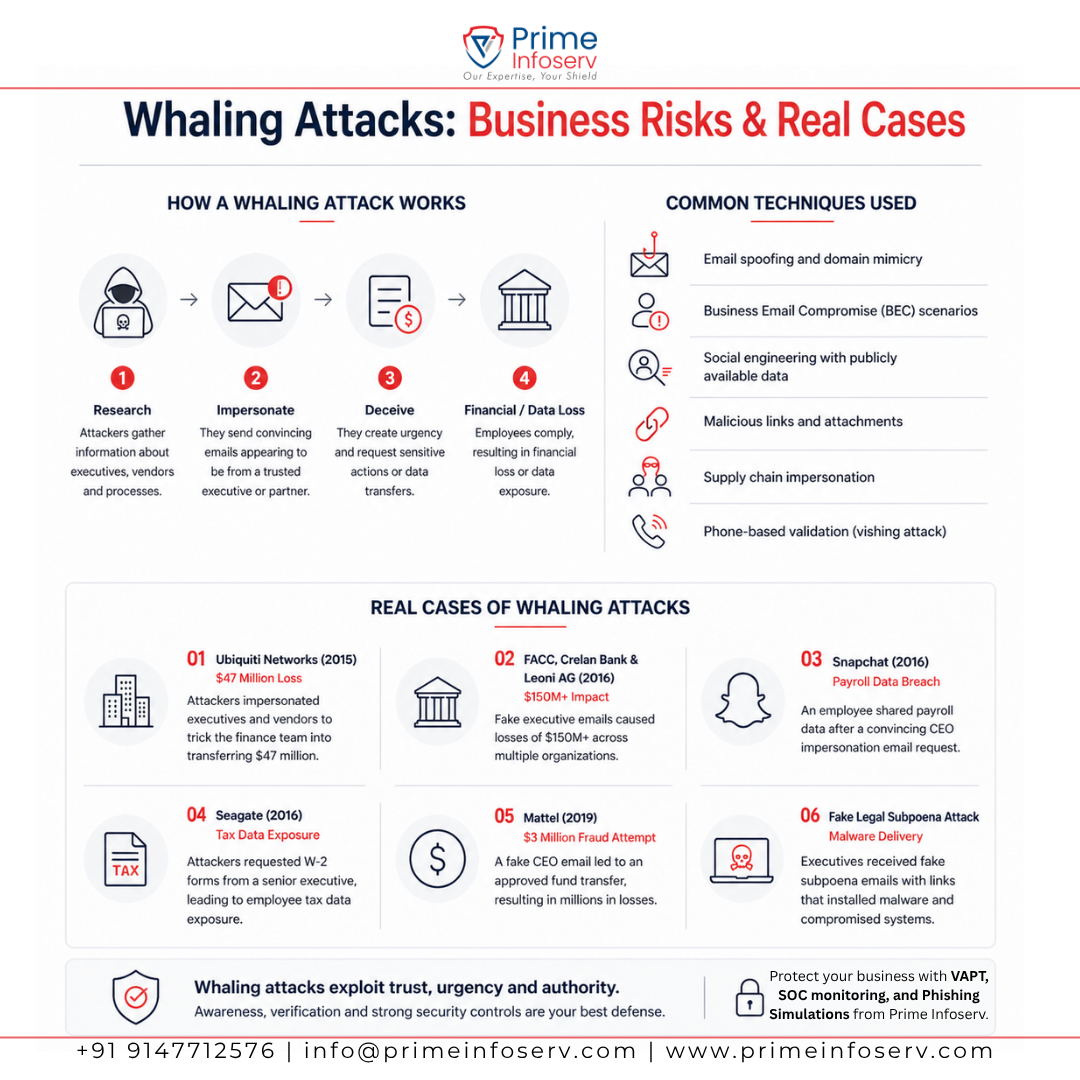
How a Whaling Attack Works
- Research: Collect data from LinkedIn, websites, and social media
- Impersonation: Spoof executive identities or domains
- Personalization: Craft realistic, context-aware messages
- Execution: Request payments, data, or access
- Reinforcement: Use vishing attacks (phone calls) to validate requests
Common Techniques Used
- Email spoofing and domain mimicry
- Business Email Compromise (BEC) scenarios
- Social engineering with publicly available data
- Malicious links and attachments
- Supply chain impersonation
- Phone-based validation (vishing attack)
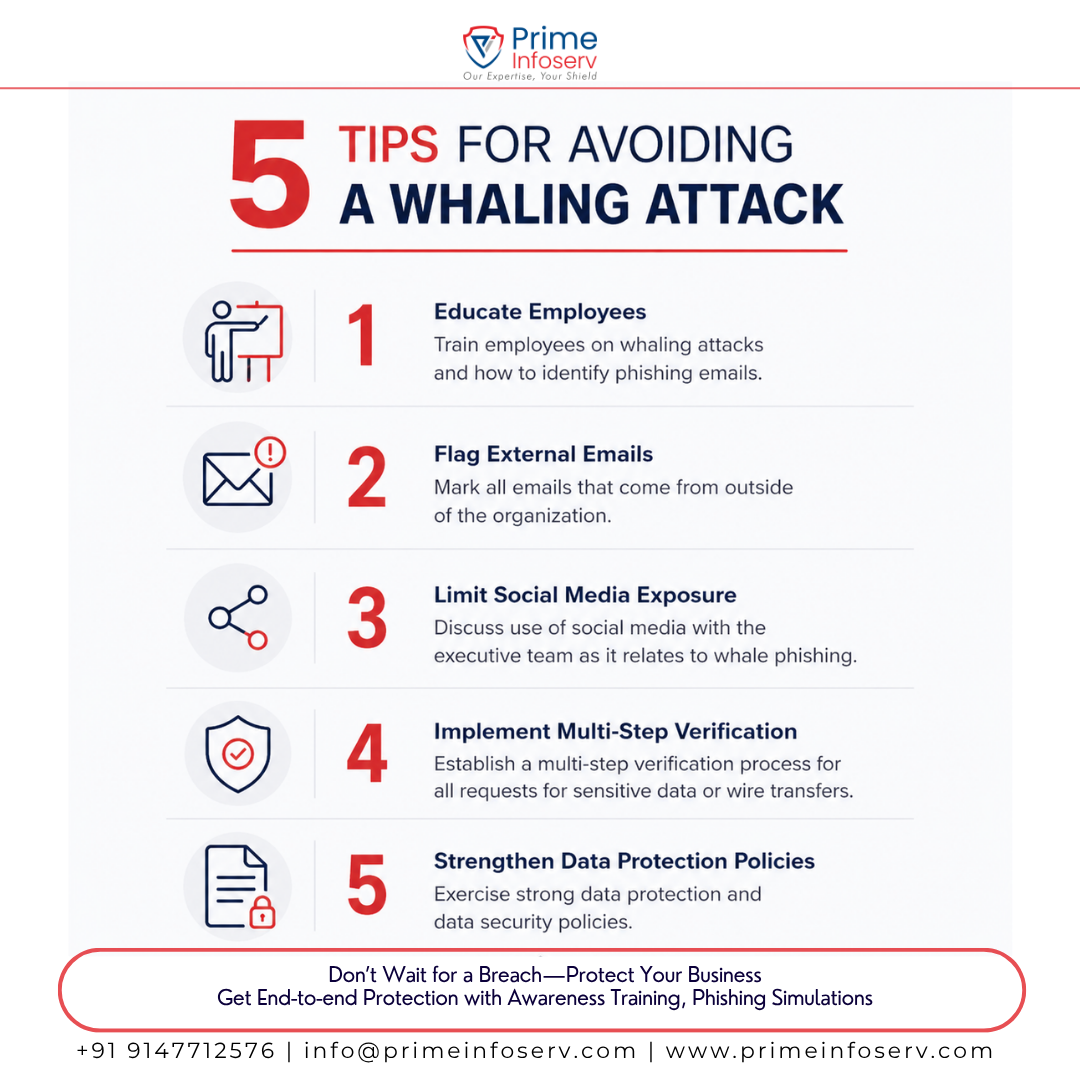
How to Prevent Whaling Attacks
- Enforce multi-level approval for payments
- Implement SPF, DKIM, DMARC email security
- Conduct executive-level awareness training
- Restrict sensitive information exposure online
- Verify requests through secondary communication channels
How Prime Infoserv Can Help
At Prime Infoserv, we help organizations defend against advanced threats like whaling phishing and BEC attacks through:
- Security Awareness Training (focused on executives)
- Phishing & Whaling Simulations
- Advanced Email Security Solutions
- Vulnerability Assessments
- Data Loss Prevention (DLP)
Build a security-first culture and reduce the risk of costly human errors. Call us today : +91 9147712576 or mail : info@primeinfoserv.com