Brazil’s Pix Users Hit by Advanced APK Malware.
Brazil is an appealing target to attackers because it has one of the most advanced mobile banking ecosystems in the world—and naturally, cyberattacks here have evolved just as rapidly. A new campaign known as PixRevolution highlights this shift, using advanced APK malware and social engineering to target users of the country’s widely used Pix instant payment system.
How the Attack Begins
The attack typically enters through trickery and social engineering. Users are lured to fake app download pages that look identical to trusted brands or local services. These pages are often perfect replicas, making them extremely difficult to distinguish from legitimate sources.
Instead of downloading a genuine app, the user unknowingly installs a malicious APK file—an Android Trojan disguised as a safe application.
What Happens After Infection
Once installed, the malware requests special permissions under the guise of normal functionality. If granted, it gains deep access to the device, including:
- Taps and swipes
- All on-screen text
- Microphone audio
- Full screen visibility
At this stage, the mobile banking Trojan effectively takes control of the device.
Real-Time Monitoring & Attack Execution
What makes this attack particularly advanced is its real-time screen surveillance capability.
The malware remains silent in the background, continuously monitoring user activity—either through automated systems or human operators. It does not act immediately.
Instead, it waits.
The moment a user initiates a payment through Pix, the attacker steps in at precisely the right time and diverts the transaction to a fraudulent account. This entire process happens within seconds, often without raising suspicion.
What Researchers Zimperium’s zLabs Found about Pix Revolution
Researchers from Zimperium’s zLabs team identified this campaign as a targeted effort against Brazil’s financial ecosystem. According to malware analyst Aazim Yaswant, the Trojan is specifically designed to exploit Pix and, indirectly, most Brazilian financial institutions.
Security experts also highlight that such attacks are increasing globally. As noted by Kern Smith, VP of global solutions engineering at Zimperium:
Large numbers of users rely on mobile apps for everyday banking and payments, creating a high-value attack surface. Many cybercrime groups have adapted their techniques as financial activity shifts to smartphones.
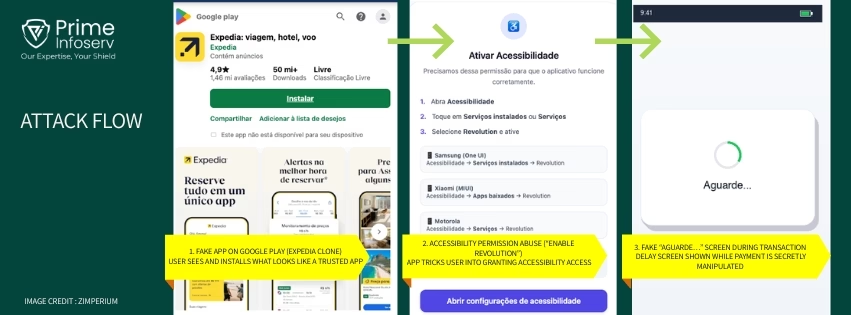
Modus Operandi (Attack Flow) of Pix Revolution apk malware
- Fake app pages mimic trusted platforms: Attackers create near-perfect replicas of trusted brands (like Expedia or postal services), often posing as official app store pages.
- User downloads a malicious APK (not from real Google Play): Instead of installing from the actual Play Store, users unknowingly download a Trojanized APK from attacker-controlled sites.
- App requests accessibility permissions (“Enable Revolution”): The app tricks users into enabling a fake accessibility service under the guise of required functionality.
- Malware gains deep device control: Once enabled, it can monitor taps, read screen content, capture inputs, and even access audio—effectively taking over the device.
- Connection established with C2 server (port 9000): The malware connects to a remote server, enabling attackers to view the screen and interact with the device in near real time.
- Continuous monitoring of on-screen activity: It scans for financial keywords (especially Pix-related terms) and tracks user behavior silently.
- Waits for a Pix payment attempt: The malware remains dormant until a transaction is initiated—this is key to its stealth.
- Attacker intervenes in real time (human/AI-assisted):At the exact moment of transaction, an operator or automated agent prepares to hijack the payment.
- Fake “Aguarde…” (Please wait) screen displayed: A delay overlay is shown to distract the user while the manipulation happens in the background.
- Funds are silently redirected: The transaction is altered within seconds and diverted to attacker-controlled accounts.
List of the brands and services impersonated by the PixRevolution malware campaigns:
- Expedia – Travel booking (flights, hotels, trips)
- Sicredi – Brazilian banking cooperative
- Brazilian Postal Service – National mail service
- XP Investimentos – Investment/brokerage platform
- Superior Court of Justice – Brazil’s Supreme Court equivalent
- Local waste collection services – Small-scale municipal trash collection
- Regional waste collection services – Larger regional trash services
- AVG Antivirus – Security software
- Pilates at Home / Fitness App – Health and wellness
Targeted Financial Institutions– The malware targets 9 major Brazilian banks/payment platforms using hardcoded logos:
- Nubank
- Itaú Unibanco
- Banco do Brasil
- Caixa Econômica Federal
- Santander Brasil
- PicPay
- PagSeguro
- Sicredi
- XP Investimentos
Why This Matters Beyond Brazil
While this attack targets Brazil’s Pix system, the technique is globally relevant. Countries like India, where digital payments and mobile banking are widespread, could face similar threats. The combination of APK malware, social engineering, and real-time monitoring makes this a scalable and dangerous model.
Staying Cautious!!!
Users should be mindful even when a website or app looks legitimate. Warning signs include:
- Being redirected to download apps outside official stores
- Requests for unusual permissions (especially accessibility access)
- Slight differences in website URLs or app listings
How Prime Infoserv Can Help
With threats like PixRevolution targeting mobile devices, securing applications is critical.
Prime Infoserv delivers Mobile Application Penetration Testing (MAPT) to uncover vulnerabilities that could enable malware-driven attacks and real-time payment fraud. Call: +91 9147712576 or mail : info@primeinfoserv.com to talk to our expert.