You’re staring at your monitor, and there it is—the 250th alert of the day. Honestly, it’s not even that important. But alerts keep piling up, day after day, week after week. After a while, do you stop treating each one with urgency? Or do you just start clicking through, hoping nothing critical slips by? This is exactly how alert fatigue creeps in, and thus due to Alert Fatigue in Security Operations (SOC)even serious threats can get missed. Can Too Many Alerts Pose a Security Risk? Find Out in This Blog.
Modern organizations rely on multiple cybersecurity tools to detect threats. Systems like SIEM, Endpoint Detection and Response (EDR), intrusion detection tools, cloud security monitoring, and identity security platforms constantly generate alerts when suspicious activity is detected.
These alerts are meant to help security teams detect threats early.
However, many organizations now face the opposite problem. Security Operations Center (SOC) teams often receive hundreds or even thousands of alerts every day. When analysts must go through such a large volume of notifications, it becomes difficult to identify which alerts actually matter & Important warnings can easily get buried in routine system noise.
This situation is known as Alert Fatigue in Security Operations (SOC), and it has become a serious challenge for modern cybersecurity teams.
What Is Alert Fatigue in Cybersecurity?
Alert fatigue happens when security analysts receive more alerts than they can realistically review. As stated by IBM “Alert fatigue is a state of mental and operational exhaustion caused by an overwhelming number of alerts — many of which are low‑priority, false positives, or non‑actionable.” Many alerts generated by security tools turn out to be:
- False positives
- Low-risk system activity
- Duplicate alerts coming from multiple tools
When analysts repeatedly investigate alerts that are not real threats, they slowly become desensitized to notifications. Over time, alerts may be reviewed faster or sometimes ignored entirely. The biggest risk is that a real cyberattack may be hidden among hundreds of routine alerts.
A well-known example happened during the Target data breach in 2013. Target’s security systems had actually detected suspicious activity in the network and generated alerts warning about malware. However, these warnings were not acted upon immediately.
The alerts were lost among many other security notifications that analysts were already handling. By the time the attack was fully discovered, cybercriminals had already stolen payment card data from more than 40 million customers.
This incident showed that even when organizations have strong security tools in place, alert overload can still prevent teams from responding in time.

Why SOC Teams Experience Alert Fatigue
Several operational challenges contribute to alert fatigue in modern SOC environments.
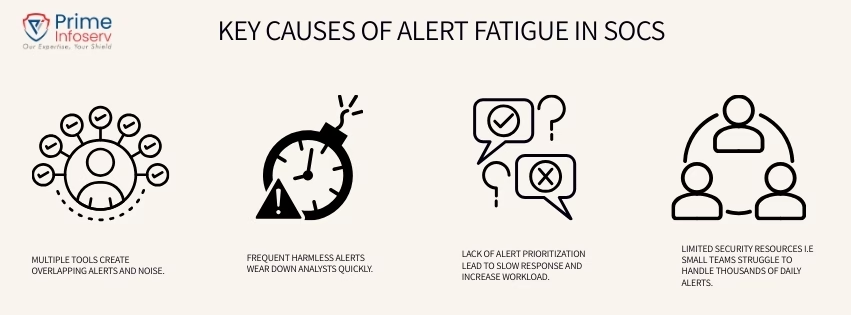
1. Too Many Security Tools
Organizations often use multiple security solutions across endpoints, networks, email, identity systems, and cloud platforms. Each tool generates its own alerts independently. This often leads to duplicate alerts and unnecessary noise.
2.High False Positive Rates
Security systems are designed to detect suspicious behavior, but many alerts turn out to be harmless activities. When analysts repeatedly investigate alerts that lead nowhere, fatigue quickly builds.
3.Lack of Alert Prioritization
Not every alert represents the same level of risk. But when alerts are not properly classified, analysts must manually determine which ones are important. This increases workload and slows down response time.
4.Limited Security Resources
Many organizations face a shortage of skilled cybersecurity professionals. A small SOC team managing thousands of alerts daily can easily become overwhelmed.
How Attackers Exploit Alert Fatigue
Cybercriminals are aware that security teams already deal with a large number of alerts. In some cases, attackers deliberately create what is known as an alert storm.
Instead of launching a single obvious attack, they trigger many alerts across different systems at the same time. This sudden flood of alerts creates confusion and overload for SOC teams. While analysts are busy reviewing the noise, the real malicious activity may continue unnoticed in the background.
This tactic can delay investigations and increase the chances of missing critical security signals.
Who Is Affected by Alert Fatigue in SOC Operations?
Alert fatigue affects multiple roles within a security organization.
- Tier-1 SOC analysts who review large volumes of low-priority alerts
- Incident response teams trying to piece together information from multiple tools
- SOC managers responsible for maintaining response times and team performance
- Security leaders who must manage complex security ecosystems and demonstrate results
Even IT and DevOps teams may experience unnecessary escalations when alerts are triggered incorrectly.
Over time, constant alert overload can lead to analyst burnout and employee turnover. When experienced team members leave, the remaining staff must handle even more work, which increases the pressure on the entire security operation.
Security Risks of Alert Fatigue
Alert fatigue can create serious cybersecurity risks for organizations. Some common consequences include:
- Delayed detection of cyberattacks
- Missed indicators of compromise
- Increased risk of ransomware or phishing attacks
- Analyst burnout and operational stress
In some cases, major security incidents happen simply because a critical alert was overlooked or investigated too late.
How Organizations Can Reduce Alert Fatigue
Organizations can reduce alert fatigue by improving how alerts are generated, prioritized, and managed. Some practical approaches include:
- Improving alert prioritization so analysts focus on high-risk threats first
- Reducing false positives through regular tuning of security tools
- Using automation and AI to filter and correlate alerts
- Centralizing security monitoring to reduce duplicate notifications
- Implementing clear SOC workflows for faster investigation and response
The goal is not to remove alerts completely, but to ensure analysts focus on alerts that truly require attention.
How Prime Infoserv Can Help Manage Thousands of Security Alerts
Managing thousands of security alerts internally can be difficult for many organizations. Prime Infoserv helps businesses strengthen their cybersecurity operations by providing:
✔ Advanced threat monitoring and alert management
✔ AI-enabled cybersecurity solutions for faster detection
✔ Reduced false positives through optimized security configurations
✔ Support for compliance and security risk management
With better visibility and smarter alert management, organizations can reduce alert fatigue and respond to threats more effectively.
Alert fatigue in Security Operations (SOC) is becoming a growing challenge as organizations deploy more security technologies.When security teams are overwhelmed by alerts, critical threats can easily go unnoticed.
Effective cybersecurity is not just about generating alerts — it is about managing them intelligently and focusing on real risks. Organizations that improve alert management, automate routine tasks, and strengthen their SOC capabilities will be far better prepared to detect and stop cyber threats before they cause serious damage.
Call us: +91 9147712576 or mail: info@primeinfoserv.com