When you hear Starkiller, you might think of the Sith apprentice from Star Wars. But this Starkiller is far more real, and far more dangerous. Starkiller is a new phishing suite designed to bypass Multi-Factor Authentication (MFA). Yes, you read that right.
It is reportedly operated by a threat group called Jinkusu and is sold as a subscription-based cybercrime platform. Criminals can simply subscribe, log into a dashboard, choose a brand to impersonate, and launch attacks — no deep technical skills required.
But Wait… Don’t We Have MFA?
Normally, MFA protects accounts by requiring:
- A password
- An OTP (One-Time Password)
- Authenticator approval
That extra step is supposed to stop attackers. So how does Starkiller bypass it?
How Starkiller Phishing Suite Bypasses MFA
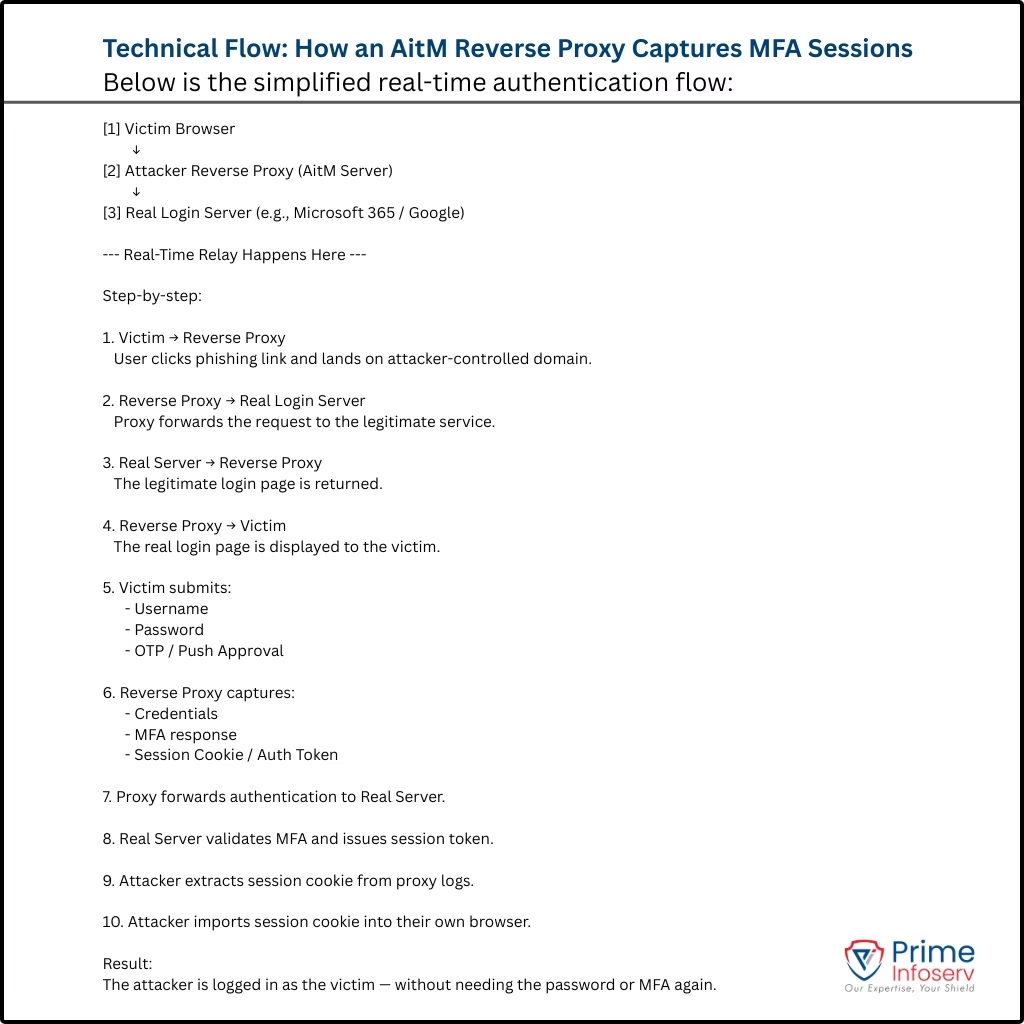
Starkiller uses something called an Adversary-in-the-Middle (AitM) reverse proxy. Here’s what that means in simple terms:
- The attacker sends you a phishing link.
- You click it.
- The page looks 100% real — because it is the real website.
But what happens is
- Your login details
- Your OTP
- Your session token
are intercepted and captured. Instead of cloning a fake website, Starkiller:
- Launches a headless Chrome browser inside Docker
- Loads the real website
- Acts as a hidden middleman between you and the real site
You log in successfully. But the attacker now has:
- Your password
- Your OTP
- Your session token (this is the key)
With the session token, they don’t need MFA again. They’re already inside.
Why Should We Be Concerned about Starkiller Phishing Suite?
Starkiller doesn’t rely on traditional fake templates. That means:
- Security tools can’t easily fingerprint it
- It stays updated automatically (because it proxies the live site)
- It uses URL shorteners like TinyURL
- Everything is managed from a central dashboard
This makes phishing:
- More scalable
- More professional
- More accessible to low-skill criminals
How to Defend Against AitM-Based MFA Bypass Attacks
1️⃣ Phishing-Resistant MFA
Normal MFA (OTP, SMS, push notification) can be intercepted in AitM attacks.
Phishing-resistant MFA means:
- Hardware security keys
- FIDO2 authentication
- Device-based login keys
These methods cannot be replayed by attackers, even if they proxy the login. Use stronger MFA that cannot be stolen through a middleman.
2️⃣ Token Binding / Device Binding
In AitM attacks, the attacker steals a session cookie.
Token binding means:
- The session works only on the original device
- If copied to another browser or system, it won’t work
Even if a hacker steals the session, they cannot use it on their own computer.
3️⃣ Conditional Access Policies
This is about adding smart login rules.
For example:
- Block login from suspicious countries
- Block unknown devices
- Detect “impossible travel” (login from India and US within minutes)
- Flag risky IP addresses
Even if someone logs in successfully, the system checks if the behavior looks normal.
4️⃣ Continuous Session Monitoring
Most systems only check security during login. Continuous monitoring means:
- Keep checking the session after login
- If something suspicious happens, log the user out
5️⃣ User Awareness: URL Inspection
In AitM attacks:
- The page looks real
- The login works
- MFA works
Only the URL shows the truth. So users must:
- Check spelling of the domain
- Avoid clicking unknown email links
- Verify login links carefully
Emerging Phishing Variants You Should Know About
a. 1Phish Phishing Kit: An MFA-Focused Threat
Another phishing kit, 1Phish, has evolved to:
- Target users of 1Password
- Capture OTPs
- Capture recovery codes
- Use browser fingerprinting to block bots
- Add anti-analysis protections
Attackers are now iterating their tools like real software companies.
b. Microsoft OAuth Device Login Abuse
In another sophisticated technique, attackers are exploiting the OAuth device login flow used by Microsoft for Microsoft 365 accounts.
Here’s how it works:
- The attacker generates a device code.
- The victim receives a phishing email.
- The victim is told to visit: microsoft.com/devicelogin (a real Microsoft domain).
- The victim enters the attacker-provided code.
- Microsoft issues a legitimate access token.
The attacker now has persistent access. This attack is especially dangerous because:
- The victim logs into a real Microsoft website
- No fake page is used
- MFA does not stop it
Conclusion:
With increasing AitM-based phishing attacks, continuous session monitoring is no longer optional for regulated institutions. Prime Infoserv delivers:
• 24/7 SOC Monitoring
• SIEM/SOAR-driven threat detection
• EDR/XDR deployment
• Identity risk and access control strategy
Let’s strengthen your cyber resilience before attackers exploit the gap. Connect with us.





