In today’s interconnected telecom ecosystem, SS7 Network Vulnerabilities expose a critical yet invisible risk to mobile users worldwide. Unlike traditional hacking, this threat operates at the network level—allowing attackers to track users without ever touching their devices. By exploiting weaknesses in global telecom infrastructure, hackers can silently monitor location data across borders.
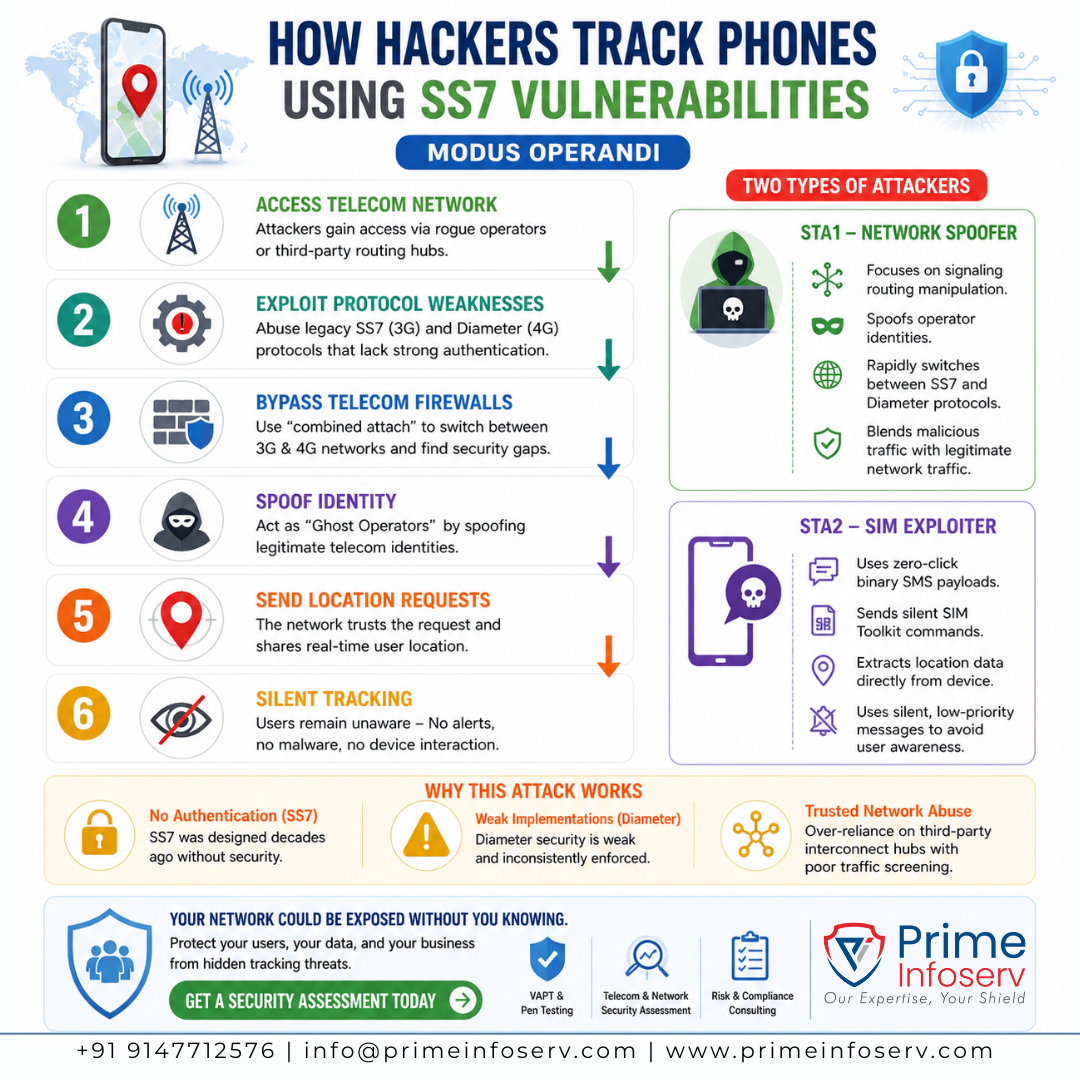
The Modus Operandi: How the Attack Actually Works
A major investigation by Citizen Lab revealed that sophisticated threat actors are exploiting fundamental weaknesses in global mobile networks to conduct large-scale surveillance.
Step-by-Step Attack Flow
- Attackers abuse legacy 3G SS7 and 4G Diameter signaling protocols
- They bypass telecom firewalls by exploiting weak or missing authentication
- Using combined attach procedures, they force devices to connect to both 3G and 4G networks
- This allows seamless switching between SS7 and Diameter to find security gaps
- Attackers manipulate routing data to disguise themselves as legitimate telecom operators
- The network unknowingly shares real-time location data of users
These attackers act as “Ghost Operators”, masking their identity while tracking high-value targets globally.
Two Types of Threat Actors Identified
STA1 – Network Spoofer
- Focuses on signaling routing manipulation
- Spoofs legitimate telecom operator identities
- Rapidly switches between SS7 and Diameter protocols
- Blends malicious traffic with normal network activity to avoid detection
Result: Silent, large-scale location tracking without touching the device
⚠️ STA2 – SIM Exploiter
- Uses a more invasive hybrid approach
- Combines SS7 network probing with zero-click binary SMS attacks
- Sends silent SIM Toolkit commands to extract location data
- Uses low-priority messages that don’t trigger alerts on the phone
Result: Direct device-level data extraction without user awareness
Why These Attacks Are Possible
These global attacks exist due to structural flaws in telecom systems:
- SS7 Protocol: No authentication mechanism
- Diameter Protocol: Weak and inconsistent security implementation
- Heavy reliance on trusted interconnect networks
- Poor traffic filtering by third-party telecom routing hubs
In simple terms: telecom networks still operate on outdated trust models
How to Prevent or Reduce the Risk
While users cannot directly fix telecom protocols, you can still minimize exposure:
For Individuals
- Avoid publicly sharing your phone number
- Use encrypted communication apps wherever possible
- Keep your phone updated with latest security patches
- Disable unnecessary SIM toolkit or carrier-based services
- Be cautious of unusual network behavior (sudden signal drops, etc.)
For Organizations & Telecom Providers
- Implement advanced telecom firewall protection
- Monitor signaling traffic for anomalies
- Conduct regular VAPT and telecom security assessments
- Reduce dependency on untrusted interconnect hubs
- Enforce stronger authentication mechanisms
How Prime Infoserv Can Help
At Prime Infoserv, we help organizations uncover and mitigate hidden risks within their network and telecom infrastructure.
Our Key Services
- Vulnerability Assessment & Penetration Testing (VAPT)
- Telecom & Network Security Assessments
- Cybersecurity Maturity Assessments
- Compliance & Risk Consulting (ISO 27001, SOC 2, etc.)
What We Deliver
- Identification of risks like SS7 Network Vulnerabilities
- Proactive threat detection strategies
- Strengthened telecom and infrastructure security
- Compliance-ready security frameworks
Final Takeaway
The findings from Citizen Lab highlight a serious global issue—mobile users can be tracked without any direct interaction or warning. As long as telecom networks rely on outdated trust-based systems, these risks will persist.
Understanding these threats is the first step toward building a more secure digital environment. Call us for a free consultation : +91 9147712576 or mail: info@primeinfoserv.com

