What Is Endpoint Security and Why Businesses Need EDR & XDR
The Antivirus Is Not Dead. But It Is No Longer Enough. Here is a conversation happening inside most enterprise security teams right now. It is not about whether the organisation needs better endpoint protection. It is about whether leadership understands why the tools they approved five years ago are quietly failing them.
Traditional antivirus software was built for a different era. It was designed to catch known threats — malware with recognisable signatures, viruses that had been catalogued and classified. For that era, it worked. Today, it catches roughly half the threats it faces. The other half walk straight through.
The shift from Antivirus to Endpoint Detection and Response (EDR), and now to Extended Detection and Response (XDR), is not a technology upgrade. It is a fundamental change in how organisations think about threat detection, investigation, and response.
Antivirus asks: have I seen this threat before? EDR asks: is this behaviour suspicious? XDR asks: what is happening across the entire environment right now?
Understanding that distinction — and why it matters — is the starting point for any serious conversation about endpoint security in 2025 and beyond.
Why Traditional Antivirus No Longer Holds the Line ?
Antivirus works by matching files against a database of known malware signatures. When a threat matches a known signature, it is blocked. When it does not match, it passes through unchallenged.
Attackers figured this out a long time ago. The result is an entire ecosystem of evasion techniques that have made signature-based detection increasingly unreliable.
Real-World Example: The SolarWinds Attack (2020)
Attackers inserted malicious code into a legitimate software update from SolarWinds, a widely trusted IT management vendor. The code was signed with a valid certificate, exhibited no known malicious signatures, and was distributed to over 18,000 organisations — including US government agencies and Fortune 500 companies. Traditional antivirus solutions across these environments raised no alerts. The breach went undetected for nine months.
SolarWinds was not an isolated incident. It demonstrated a pattern that has become standard in sophisticated attacks:
- Attackers use legitimate tools and signed code to avoid signature detection
- Malware is polymorphic — it changes its signature with each infection to evade matching
- Fileless attacks operate entirely in memory, leaving no file on disk for AV to scan
- Living-off-the-land techniques abuse legitimate system processes like PowerShell and WMI
Antivirus was never designed to detect these behaviours. It was designed to recognise files. That gap is no longer theoretical. It is operational, and organisations are paying for it.
What Does Endpoint Detection and Response (EDR) Do and Why Is It Important?
What Endpoint Detection and Response (EDR) Changes — and Why It Matters: Endpoint Detection and Response was built around a different premise. Rather than matching threats to known signatures, EDR continuously monitors behaviour on every endpoint — every process started, every file touched, every network connection made, every registry key modified.
When a pattern of behaviour looks suspicious — even if the individual components are not malicious in isolation — EDR raises an alert, records the full context, and gives security teams the ability to investigate and respond in real time.
Real-World Example: The Colonial Pipeline Attack (2021)
Attackers gained access through a compromised VPN account with no multi-factor authentication. Once inside, they moved laterally across the network, deployed ransomware, and forced the shutdown of a pipeline supplying 45% of the US East Coast’s fuel. A mature EDR deployment monitoring lateral movement patterns and unusual process behaviour could have detected the intrusion during the reconnaissance phase — days before the ransomware executed.
The capabilities EDR adds over traditional antivirus are substantial:
- Behavioural analytics — detects anomalous activity even from unknown threats
- Full attack timeline — reconstructs the complete sequence of events leading to an incident
- Threat hunting — allows security teams to proactively search for indicators of compromise
- Automated response — isolates compromised endpoints, kills malicious processes, rolls back changes
- Forensic depth — captures the evidence needed for post-incident investigation and regulatory reporting
For organisations that experienced a serious incident while relying on traditional antivirus, the shift to EDR often feels less like an upgrade and more like turning the lights on in a dark room.
What Is Extended Detection and Response (XDR) and How Does It Improve Security?
Where Extended Detection and Response (XDR) Goes Further — The Unified Picture : EDR is powerful. But it has a boundary. It sees everything happening on an endpoint. It does not see what is happening across the network, in cloud workloads, in email systems, or in identity platforms — and attackers rarely confine themselves to a single layer.
Extended Detection and Response (XDR) breaks that boundary. It ingests telemetry from endpoints, network, cloud, email, and identity systems into a unified detection and response platform. Instead of investigating five separate alerts across five separate tools, security teams see a single, correlated attack story.
XDR does not give you more alerts. It gives you fewer, better ones — with the full context to act on them decisively.
This matters because alert fatigue is one of the most underestimated risks in enterprise security. Organisations with large security toolsets often generate thousands of alerts per day. Most are noise. Some are critical. Without correlation, telling the difference requires significant analyst time — time that most teams do not have.
XDR reduces that burden by connecting the dots automatically. An unusual login at 2am, followed by a lateral movement attempt, followed by a large data transfer to an external IP — three events that might appear as separate low-priority alerts in isolated tools — become a single high-confidence incident in XDR.
Real-World Example: The MOVEit Breach (2023)
The Cl0p ransomware group exploited a zero-day vulnerability in the MOVEit file transfer software, exfiltrating data from hundreds of organisations globally before a patch was available. Organisations with XDR platforms monitoring unusual data movement patterns — including large outbound transfers and access to sensitive file repositories outside normal business hours — were able to detect and contain the exfiltration significantly faster than those relying on endpoint-only tools.
AV vs EDR vs XDR: What Each Actually Delivers
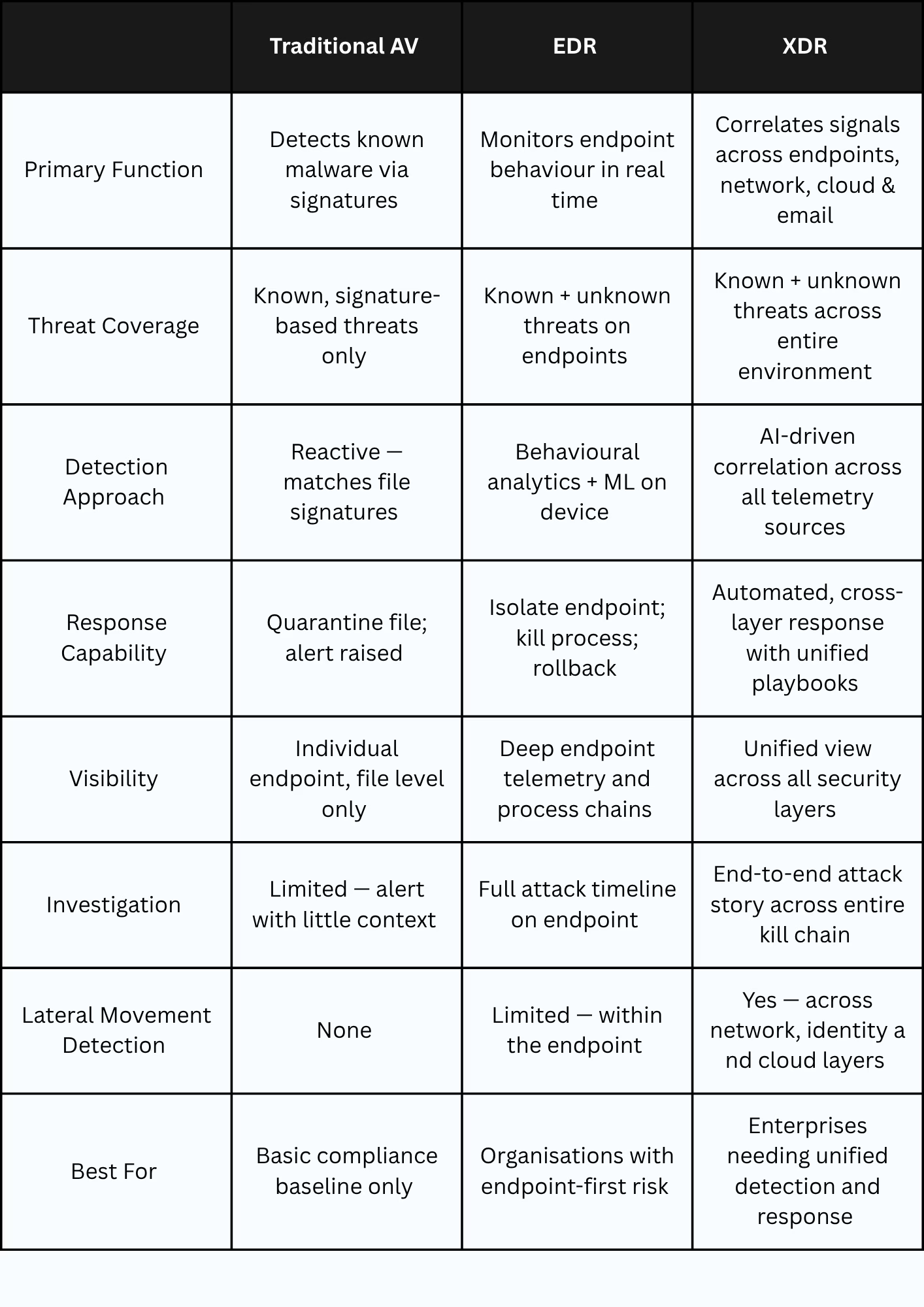
The table above is not an argument for replacing everything immediately. It is a map of what each layer provides — and where the gaps are. Most organizations today have antivirus. Many are beginning to deploy EDR. Fewer have unified their security telemetry under XDR. Understanding where you sit on that spectrum is the starting point for a rational investment conversation.
Steps to Transition from Antivirus to EDR and XDR
How Organisations Should Approach the Transition :The move from antivirus to EDR to XDR is not a one-time decision. It is a maturity journey that should be sequenced deliberately, not rushed.
Stage 1 — Baseline Coverage
Ensure every endpoint in the environment has antivirus in place. This is not a security strategy. It is a compliance baseline. If this step is incomplete, EDR deployment will be inconsistent.
Stage 2 — EDR Deployment
Deploy EDR across all endpoints — servers, workstations, and where possible, cloud workloads. Prioritise visibility before response automation. Understand what normal looks like in your environment before tuning alerting thresholds. Many organisations underestimate how much noise an out-of-the-box EDR deployment generates before it is properly calibrated.
Stage 3 — Integration and Correlation
Begin connecting EDR telemetry to other data sources — network logs, identity platforms, cloud security tooling, email security. This is the foundation of XDR. Even without a dedicated XDR platform, correlation between tools dramatically improves detection quality.
Stage 4 — XDR or Managed Detection and Response
For organisations with the analyst capacity to operate a unified platform, XDR delivers the most complete picture. For those without a mature internal security operations capability, Managed Detection and Response (MDR) provides XDR-level coverage through an external partner — often a more practical starting point.
The goal is not to buy the most advanced tool. The goal is to close the gaps that attackers are already exploiting in your current environment.
What CXOs and CISOs Need to Decide on EDR vs XDR Adoption
The transition from antivirus to EDR to XDR ultimately requires leadership to answer three questions that tools alone cannot answer.
First: What is our current detection gap?
Most organisations cannot answer this. They know what their tools alert on. They do not know what is passing through undetected. A threat assessment or red team exercise is often the fastest way to make this visible.
Second: Do we have the capacity to act on what we detect?
EDR generates significantly more data and alerts than antivirus. XDR generates more still. Without a security operations function — internal or external — that capacity goes to waste. Buying the tool without the operational model to support it is a common and expensive mistake.
Third: What is the cost of not acting?
Quantifying cyber risk in financial terms is difficult, but not impossible. Average breach costs, regulatory penalties, operational downtime, and reputational impact all have calculable ranges. Framing the investment in those terms makes the conversation with boards and finance committees substantially more productive.

The Executive Takeaway
Traditional antivirus is not a security strategy. It is a starting point — one that most enterprise threat actors have long since learned to bypass.
- EDR gives organisations the visibility and response capability that modern threats require
- XDR connects that visibility across every layer of the environment, eliminating the blind spots attackers exploit between tools
- The transition is a maturity journey, not a single purchase — sequencing matters as much as selection
- Operational readiness — the ability to investigate and respond — is as important as the technology itself
Organisations that make this transition deliberately, with the right operational model in place, build the detection and response capability that modern enterprise threats demand. Those that remain on antivirus alone are not managing risk. They are deferring the consequences of it.
FAQs
1. Is traditional antivirus completely obsolete?
Not completely — antivirus still provides a baseline layer of protection against known threats and remains a compliance requirement in many frameworks. However, it is insufficient as a standalone security measure against modern attacks. It should be treated as the floor, not the ceiling, of endpoint protection.
2. What is the difference between EDR and XDR?
EDR (Endpoint Detection and Response) focuses on monitoring and responding to threats at the endpoint level. XDR (Extended Detection and Response) extends that capability across multiple layers — endpoints, network, cloud, email, and identity — correlating signals from all sources into a unified detection and response platform.
3. How long does an EDR deployment typically take?
A basic EDR deployment across a mid-sized enterprise typically takes 4 to 12 weeks, depending on environment complexity, number of endpoints, and the time required to tune alerting thresholds to reduce noise. The technical deployment is often faster than the operational readiness work that follows.
4. Do we need a dedicated security operations centre (SOC) to use EDR or XDR?
Not necessarily. Many organisations use Managed Detection and Response (MDR) providers to operate EDR and XDR capabilities on their behalf. This is often the most practical path for organisations that lack a dedicated internal security operations team.
5. How does Zero Trust relate to EDR and XDR?
Zero Trust and EDR/XDR are complementary architectures. Zero Trust governs who and what is allowed to access resources by enforcing continuous verification of identity and device posture. EDR and XDR monitor what happens after access is granted — detecting suspicious behaviour even from authenticated users. Together, they address the two most common attack vectors: compromised credentials and endpoint-based intrusion.
Prime Infoserv Cybersecurity Practice
Prime Infoserv’s cybersecurity team helps organisations assess, modernise, and operate their security capabilities — from endpoint protection and SOC design to Zero Trust architecture and compliance. We work with enterprises to close the gap between the tools they have and the protection they need. Secure your security posture today. Call +91 9147712476, Mail: info@primeinfoserv.com