The Stryker Cyber Attack on March 11, 2026, caused widespread disruption across Stryker Corporation’s global networks.The incident affected the company’s Microsoft environment, limiting access to several internal systems used across its worldwide operations.
The Michigan-based company, which employs over 56,000 people and operates in 61 countries, disclosed the incident publicly and acknowledged that the attack caused system disruptions and restricted access to some platforms, while recovery efforts were underway.
What Does Stryker Corporation Do?
Stryker Corporation is one of the world’s leading medical technology companies. The organization develops and manufactures equipment used by hospitals, surgeons, and healthcare providers worldwide.
The company’s core areas include:
- Orthopedic implants and surgical equipment
- Medical and surgical technologies
- Hospital beds and patient handling systems
- Neurosurgical and spine care devices
- Digital healthcare technologies
Because of its global role in supplying medical technology to healthcare providers, disruptions affecting the company can have wider implications for healthcare supply chains and hospital operations.
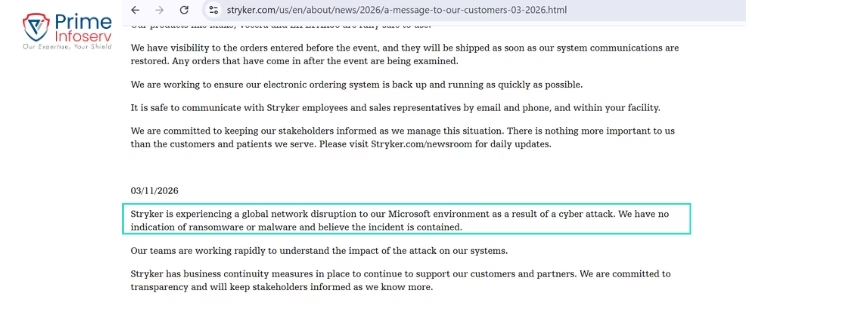
Official Confirmation of the Stryker Cyber Attack
On March 11, 2026, the company acknowledged the incident on its official platform and stated that a cyber attack had caused disruption to its internal network systems.
The company shared the following statement:
“Stryker is experiencing a global network disruption to our Microsoft environment as a result of a cyber attack. We have no indication of ransomware or malware and believe the incident is contained.
Our teams are working rapidly to understand the impact of the attack on our systems.
Stryker has business continuity measures in place to continue to support our customers and partners. We are committed to transparency and will keep stakeholders informed as we know more.”
The company also confirmed that business continuity plans were activated to ensure ongoing support for healthcare customers and partners.
Key Facts About the Stryker Cyber Attack Incident
| Category | Details |
|---|---|
| Company | Stryker Corporation |
| Industry | Medical Technology |
| Headquarters | Michigan, United States |
| Employees | 56,000+ |
| Global Presence | Operations in 61 countries |
| Date of Attack | March 11, 2026 |
| Attack Type | Destructive wiper malware attack (reported by security experts) |
| Threat Actor | Handala |
| Ransom Demand | No ransomware request reported |
| System Status | Restoration timeline still unknown |
Who Is the Handala Hacking Group
Cybersecurity researchers linked the attack to Handala, a pro-Palestinian hacktivist group believed to have connections to Iranian cyber activity.
The group reportedly:
- Claimed responsibility via Telegram
- Displayed the Handala logo on compromised login pages
- Conducted the operation as part of a politically motivated cyber campaign
Hacktivist groups like Handala often launch attacks aimed at sending political messages or disrupting organizations linked to geopolitical conflicts.
Why Handala Hackers Targeted Stryker
According to statements attributed to the attackers, the Stryker corporation cyber attack was carried out as retaliation for an alleged bomb strike on a school in Minab, Iran on 28th Feb 2026.

Security experts believe the attack is part of a broader trend where companies become indirect targets during geopolitical tensions, even when they are not directly involved in the conflict.
How the Cyber Attack of Stryker Was Carried Out
Initial investigations suggest that attackers gained access through administrative credentials, which allowed them to move across internal infrastructure.
Once inside the network, they reportedly:
- Defaced system login pages
- Deployed wiper malware designed to erase data
- Remotely wiped corporate systems and connected devices
Unlike ransomware attacks that demand payment, wiper malware attacks are designed to destroy systems and cause operational disruption.
Operational Impact of the Stryker Cyber Attacks
The cyber incident affected multiple operational areas within the organization.
Operational Impact Summary
| Impact Area | Details |
|---|---|
| System Access | Employees unable to access internal platforms |
| Login Infrastructure | Compromised login pages displaying attacker messages |
| Data Integrity | Malware reportedly designed to erase corporate data |
| Endpoint Devices | Corporate laptops and connected devices affected |
| Workforce Impact | 5,500+ employees in Cork, Ireland impacted |
| Engineering Operations | Product design and development activities paused |
| Global Operations | Facilities across Europe, Asia, and the U.S. experienced disruption |
| Recovery Process | Restoration efforts still ongoing |
The scale of the disruption highlights how cyber attacks can affect operational continuity across multinational companies.
Market Reaction and Stryker Share Price
The cyber incident also affected investor sentiment. After news of the attack emerged, the stryker share price experienced a decline.
Financial Impact
| Market Factor | Details |
|---|---|
| Stock Reaction | Stryker share price dropped about 3.6% |
| Investor Sentiment | Concerns over operational disruptions |
| Corporate Risk | Cybersecurity incidents increasingly impact market confidence |
| Financial Impact | Major breaches can affect company valuation |
The drop in stryker share price demonstrates how cybersecurity incidents can rapidly influence financial markets and investor perception.
What This Attack Reveals About Modern Cyber Threats
The cyber attack on Stryker highlight how cyber operations are increasingly used as tools for geopolitical influence and economic disruption.
Key trends highlighted by this incident include:
| Cybersecurity Trend | Explanation |
|---|---|
| Geopolitical Cyber Warfare | Corporations becoming targets during international conflicts |
| Destructive Malware | Attacks focused on data destruction instead of extortion |
| Economic Disruption | Cyber operations designed to disrupt business activity |
| Expanding Threat Landscape | Global organizations facing increased cyber risk |
Security researchers warn that Iran-linked cyber groups may increase retaliatory cyber operations against Western organizations.
Why Continuous Monitoring to Prevent Cyber Attack Is Essential
The Stryker hacked incident reinforces an important cybersecurity lesson: no organization is immune to cyber threats.
As businesses continue to expand their digital infrastructure, organizations should prioritize:
- Continuous security monitoring
- Proactive threat detection
- Effective incident response planning
- Reliable disaster recovery strategies
Strong cybersecurity practices help organizations detect threats earlier and reduce operational disruption.
Strengthen Your Cybersecurity with Prime Infoserv
Incidents like the Stryker cyber attack demonstrate how quickly cyber threats can disrupt even large global enterprises. As digitization accelerates, organizations must prepare for evolving cyber risks. At Prime Infoserv, we help organizations strengthen their security posture through:
- 24/7 Security Monitoring (SOC Services)
- Threat Detection and Incident Response
- Cybersecurity Risk Assessments
- Compliance and Security Framework Implementation
- Security Awareness and Phishing Training
Our goal is not to create fear, but to help organizations build resilience and stay prepared for modern cyber threats.
If your organization wants to strengthen its defenses and reduce the impact of future attacks, connect with Prime Infoserv for expert guidance and proactive cybersecurity solutions. Call: +91 9147712576 or mail : info@primeinfoserv.com