With the increasing sophistication of cyber threats, protecting your business has become more critical than ever. Today’s cyberattacks are largely carried out by organized hacker groups motivated by financial gain, data theft, or operational disruption. They rarely rely on advanced hacking alone—instead, they exploit human error, weak security practices, and lack of verification.
To defend against these evolving threats, businesses must adopt a layered and proactive cybersecurity approach that combines technology, processes, and employee awareness.
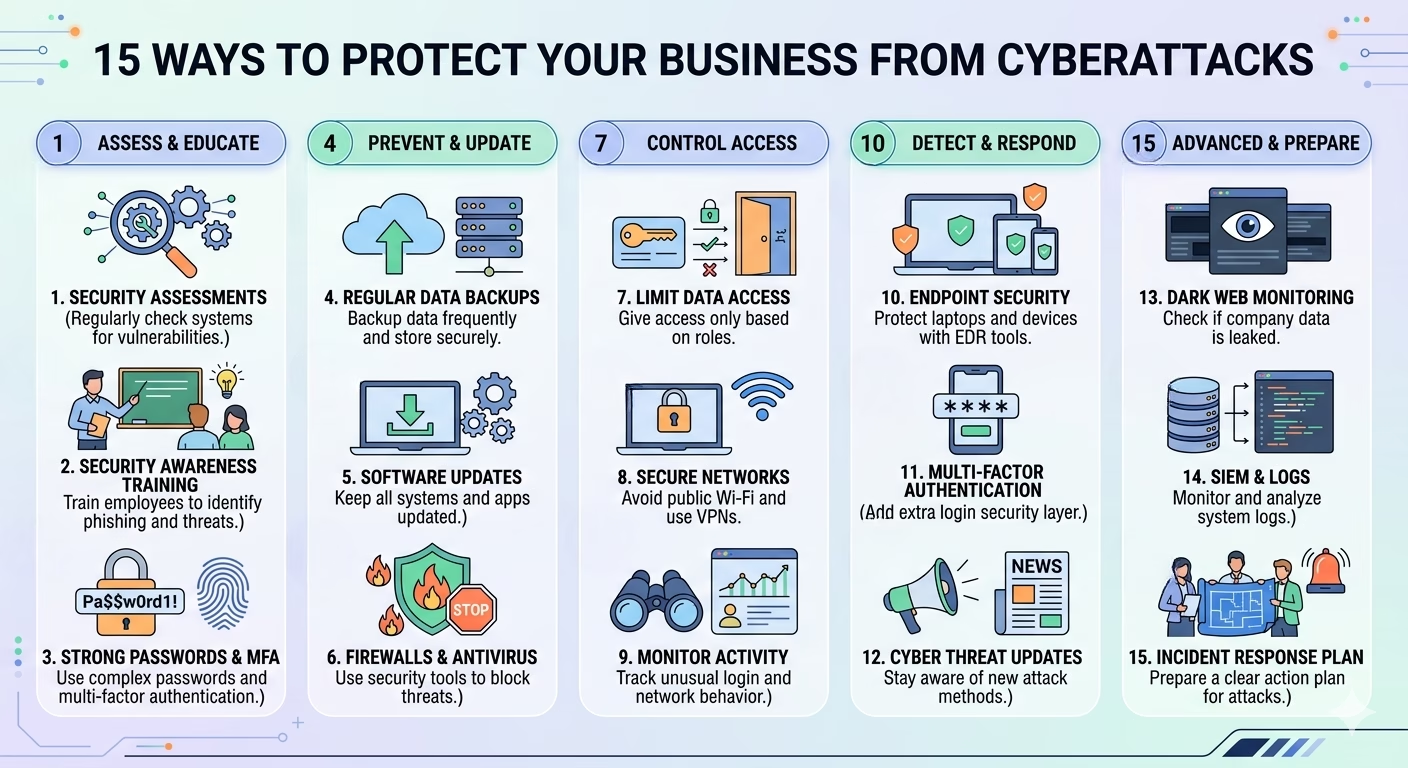
Below are 15 essential strategies every business should implement:
1. Conduct Frequent Security Assessments
Regularly evaluate your systems to identify vulnerabilities before attackers do.
- Perform internal and external security audits
- Identify and fix security gaps proactively
- Maintain a clear security baseline
2. Security Awareness Training
Employees are the first line of defense against cyberattacks.
- Train staff to recognize phishing and social engineering
- Educate them on company security policies
- Conduct regular cybersecurity awareness sessions
3. Use Strong Passwords & Authentication
Weak credentials are a major entry point for attackers.
- Enforce complex password policies
- Avoid password reuse across systems
- Enable Multi-Factor Authentication (MFA)
4. Regular Data Backups
Backups ensure business continuity during attacks like ransomware.
- Schedule automated backups
- Store backups securely (offline or encrypted cloud)
- Test recovery systems regularly
5. Keep Software Updated
Outdated systems are easy targets for cybercriminals.
- Enable automatic updates
- Apply security patches immediately
- Remove unsupported software
6. Use Firewalls & Antivirus Protection
A strong first layer of defense against external threats.
- Install enterprise-grade firewalls
- Use updated antivirus/anti-malware tools
- Monitor incoming and outgoing traffic
7. Limit Access to Sensitive Data
Not every employee needs access to all information.
- Apply Role-Based Access Control (RBAC)
- Restrict admin-level permissions
- Monitor data access logs
8. Secure Network Usage
Unsecured networks are a common attack vector.
- Encrypt all data transmissions
- Avoid public Wi-Fi for business operations
- Use secure VPN connections
9. Monitor Network Activity
Early detection helps prevent major breaches.
- Track unusual login attempts
- Monitor traffic anomalies
- Use real-time alert systems
10. Implement Endpoint Security (EDR)
Endpoints like laptops and devices are common targets.
- Deploy Endpoint Detection & Response tools
- Monitor device behavior continuously
- Respond quickly to threats
11. Use Multi-Factor Authentication (MFA)
Even if passwords are stolen, MFA blocks unauthorized access.
- Enable MFA across all critical systems
- Use app-based authentication or hardware tokens
12. Stay Updated on Cyber Threat Trends
Cyberattacks evolve constantly.
- Track emerging attack methods
- Stay informed about industry threats
- Adapt security policies regularly
13. Monitor Dark Web Exposure
Stolen data often appears on the dark web.
- Monitor leaked credentials
- Detect early signs of data breach
- Take immediate remediation actions
14. Implement SIEM & Log Management
Logs help detect and analyze attacks.
- Collect logs from all systems
- Analyze patterns for suspicious activity
- Improve compliance and incident response
15. Build a Cybersecurity Response Plan
Preparation reduces damage during an attack.
- Define incident response procedures
- Assign response roles clearly
- Conduct regular simulation drills
Cybersecurity is not a one-time setup—it is a continuous process. Businesses must combine technology, employee awareness, and proactive monitoring to stay protected against evolving threats. Read about 10 Cyber Attack Trends Businesses Must Watch in 2026 to understand how cyber threats are evolving and how to stay protected.
Strengthen Your Cybersecurity with Experts
If you want to move beyond basic protection, working with cybersecurity professionals can help you build a tailored and proactive security strategy aligned with your business needs.
Prime Infoserv, provides end-to-end cybersecurity support through:
- Governance, Risk & Compliance (GRC) services
- Managed Security Services (MSS)
- Security audits & risk assessments
- Enterprise-grade protection strategies
Protect your business before attackers exploit your weaknesses, security starts with preparation, not reaction ! Call us today :+91 9147712576 | Email: info@primeinfoserv.com